
Just out of the box
eXtensions
|
MacBookPro: Out of the Box |

As the insurance company is being nice and quick after the burglary at my house, I bought a new camera recently: a Nikon D70S, which is almost the same as the one stolen. A few days later I picked up a MacBookPro. This has the 2.16GHz Core 2 Duo processor and 120G hard disk. I had been thinking of one of these for months but my recent history meant that it came into my hands far sooner than I had planned.
As with the Mac mini, which I had been using as a temporary machine in my office, I was now going to have to switch to a new machine and rebuild the way I work: no matter how you do it, no two machines are ever the same. I started by unsealing the box, putting the packing to one side, inserting the installer disk and erasing the hard disk.
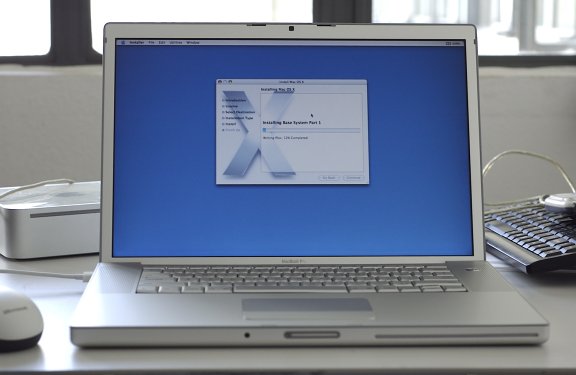
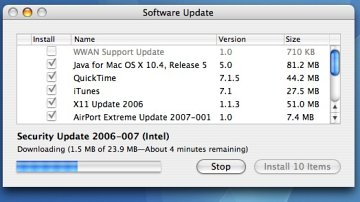
Although the disks had the latest version of the operating system (10.4.8), there were several updates to be downloaded for OS X (security) and applications. Fortunately, the office was having a good day and this part of the operation was carried out reasonably quickly.
A few applications that I had been using regularly were either not available for Macs with Intel processors or would not work, so I found substitutes. For BBEdit I now use TextWrangler; instead of MacJanitor, I downloaded Yasu.
 One of the more important downloads was Gimp (Graphics Image Manipulation Program): a substitute for Photoshop. It does not have all the features of the Adobe product, but for most users there is more than enough. This is an Open Source application like NeoOffice that I also installed.
One of the more important downloads was Gimp (Graphics Image Manipulation Program): a substitute for Photoshop. It does not have all the features of the Adobe product, but for most users there is more than enough. This is an Open Source application like NeoOffice that I also installed.
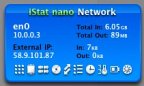 Mac Stumbler, a utility to find WiFi networks, did not want to play. A visit to Versiontracker.com found several alternatives. I tried three or four before settling on "Ap Grapher" and a widget called "MacWireless.com". The former gives me graphs and some statistics. The latter a quick panel to show what is there. I complemented this with the iStat nano widget that displays several computer functions including the Mac's IP number.
Mac Stumbler, a utility to find WiFi networks, did not want to play. A visit to Versiontracker.com found several alternatives. I tried three or four before settling on "Ap Grapher" and a widget called "MacWireless.com". The former gives me graphs and some statistics. The latter a quick panel to show what is there. I complemented this with the iStat nano widget that displays several computer functions including the Mac's IP number.
To tidy up the security, Little Snitch was installed: this reports any attempts to make connections from the computer: the sort of thing that some software companies build into their products to see how and where they are being used. Some of those outgoing transmissions are right of course. Little Snitch has a number of defaults built in and an owner can either stop or allow any other calls home: once or forever.
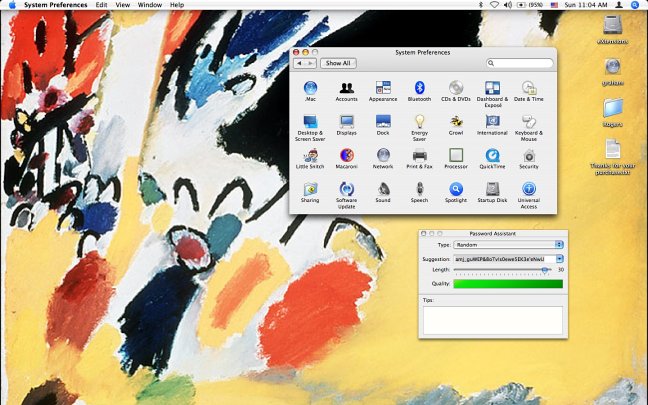
Going out is one thing; coming in needs a firewall. This was off by default, so in System Preferences I opened Sharing and turned it on. All ports are closed by default except those for essential services like mail and web browsing. As a user adds applications (for example FTP software, or MSN Messenger) so the ports for these are opened.
As on my other computers (current and lost) I created a couple of accounts. The adminstrator account, which is a must for OS X; a normal user account for myself that I work in on a day to day basis; and an open (but restricted) account with no password for anyone to use. Although my user account does not have Admin privileges, I can run almost all tasks from there, including software installations, by entering the relevant password when prompted.
I know many people hate the need to enter passwords over and over again, but it is a trade off for the better security I have. If I had had better locks for my front door, I might not be writing about this computer now, of course.
I also decided to use stronger passwords and generated these with the Password Assistant in the Accounts preferences panel. I must admit, however, these are a devil to remember; but that makes them much harder to guess or to break.
At home, I networked the notebook computer with the eMac and downloaded the data I would need for everyday use. I also copied the entire iTunes folder. I just dropped this onto the iTunes panel on the new computer and the entire library was imported in a few minutes. This allowed me to delete the music on the eMac, liberating over 5GB of much needed disk space.
As a final, personal touch, I copied the Kandinsky (Impression 3) to serve as the desktop picture as it does on the other computers I use.

For further information, e-mail to
Back to
eXtensions
To
eXtensions: 2004-05
To
eXtensions: Year Two
To
eXtensions: Year One
To
eXtensions: Book Reviews
Back to homepage