Tracking Networks and Risks on the iPhone: Available Utilities - More Misses than Hits

AMITIAE - Tuesday 20 January 2015
|
Tracking Networks and Risks on the iPhone: Available Utilities - More Misses than Hits |
 |
|
|
By Graham K. Rogers
The argument about security and surveillance is that if we are doing nothing wrong, then we should not worry. Only the terrorists or the criminal gangs, or those interested in child pornography (the arguments are cycled) are the targets. But we should worry. Forget the points about current methods and capabilities, the problems are in the future. As a former policeman, I remember pushing the limits of the law and sometimes - particularly in the early days of UK drink-drive legislation - fudging those limits. We were always kept in check, by senior officers (worried about blame) and particularly by the courts and lawyers: sometimes our arguments were accepted, sometimes not. I am grateful for that and the respect for law that it taught me. There is less assurance of those checks and balances nowadays. Indeed some of the revelations about interceptions strongly suggest laws are being ignored as a matter of course. However, it is not only the government that users could be at risk from.
This came into public awareness just a few years ago when a cell of Russian spies - years after the end of the Cold War - were arrested in the USA: dead drop boxes, chalk-marked tree stumps, the brush pass, maps, photographs were all being used (Robert Tilford, Examiner). One method of concealment that caught my eye was the way they had concealed text inside images. I found a few examples of software that I could try on the Mac and a couple for iOS devices. I wrote about these in two articles for the Bangkok Post, Database:
The best app for iOS was StegoSec and for the Mac, StegoSecOsX. An additional and major advantage was that data encrypted in one could be decrypted in the other. Although not updated these still run on current versions of the respective operating systems. They are not industrial strength applications. There is of course an ethical problem here - why hide data in such a way? - until one thinks about the actions of certain régimes, for example, Ceauscescu's typewriter registration. There are good people fighting bad authorities; only the authorities don't see it that way. And if you think that the commercially available steganography is worth trying, remember that the US authorities cracked the spies' encryption because the USA had better algorithms than the Russians. These are not industrial strength applications.
For those who have used UNIX, there are a number of such tools available baked into the operating system. Simple commands like who, whoami and ping have long been used. Not everyone is comfortable working at the command line and with the Mac the Network Utility has some of the tools but with a more user-friendly interface. With more people moving to handheld devices, utilities for these are also needed. I spoke to a young smartphone user a couple of weeks ago who does not have a computer. When I asked Why, he replied, "What's the point?"
Which brings me to GeoTCPTrace. It is not the newest tool (2010) and is in need of an overhaul. It has 5 basic tools plus About: GeoIP, Ping, Check Connection, Traceroute and Servers Monitoring. Only GeoIP worked by identifying the location of an IP number (I used one of Apple's), but the keyboard would not clear, so I was unable to view the map. Ping, Check Connection and Traceroute all crashed the app (even after I restarted the iPhone), while Servers Monitoring did not allow me to enter any data (no keyboard) and always refused to return to the main page, needing an app restart each time I tried.
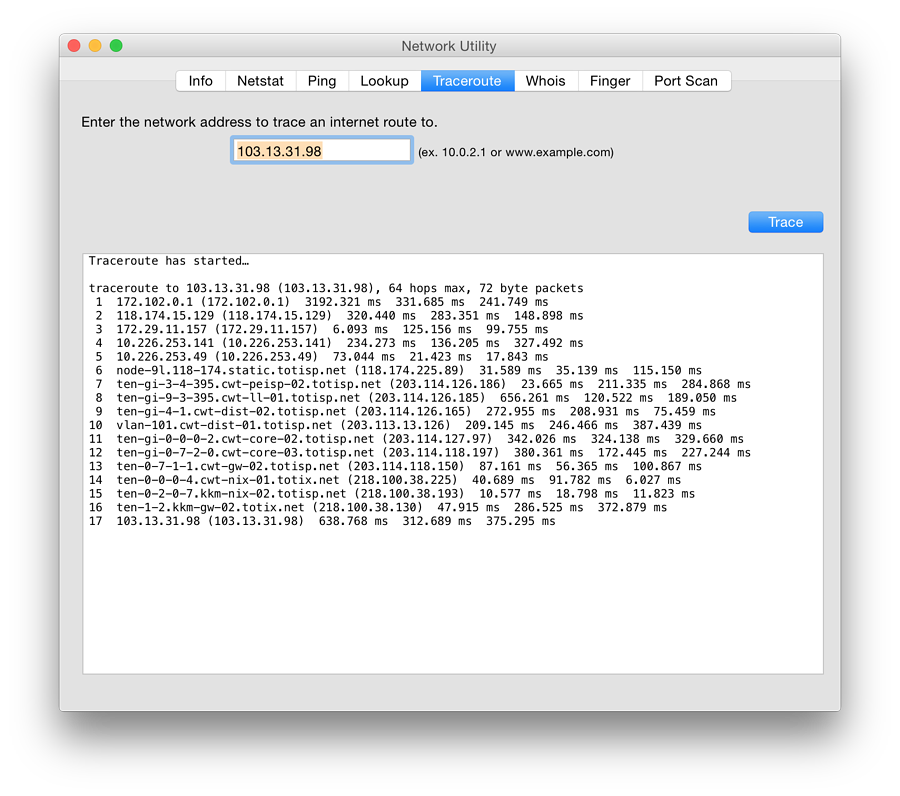
Ping and Ping Subnet were straightforward, with the latter usefully highlighting the devices it found in the subnet. Traceroute was a little less helpful. I ran this a number of times and on each try it was unable to identify several of the hops, eventually running out of steam. In comparison, the Mac version in Network Utility found my IP in 17 hops.
I was unable to make the Telnet function work. This is used less nowadays for reasons of security, and other methods are now more commonly used to make connections. I tried the same addresses I used in the Ping app on the Mac using Terminal, but was similarly unsuccessful, whereas I had been in the past. The paid version is listed at $3.99.
Although the information using the app was limited, both in terms of features and access, it does provide some ways that users may make discoveries about the environment they are working in. What is missing however are the features of Lookup and Whois, which are particularly useful when trying to identify sources of phishing emails.
Internet Connection Map - from NECTEC
I was able to identify several of the connections as Apple (IP numbers beginning with 17.x.x.x) and the app also identified email use. Facebook was also shown and certain changes were evident as I used different apps. The app is somewhat limited as it is not possible to search for IP numbers and glean other information. I was, however, able to send the data from the app via email, in CSV format. This was a little more accessible and I would be able to use other applications to track down any suspect connections.
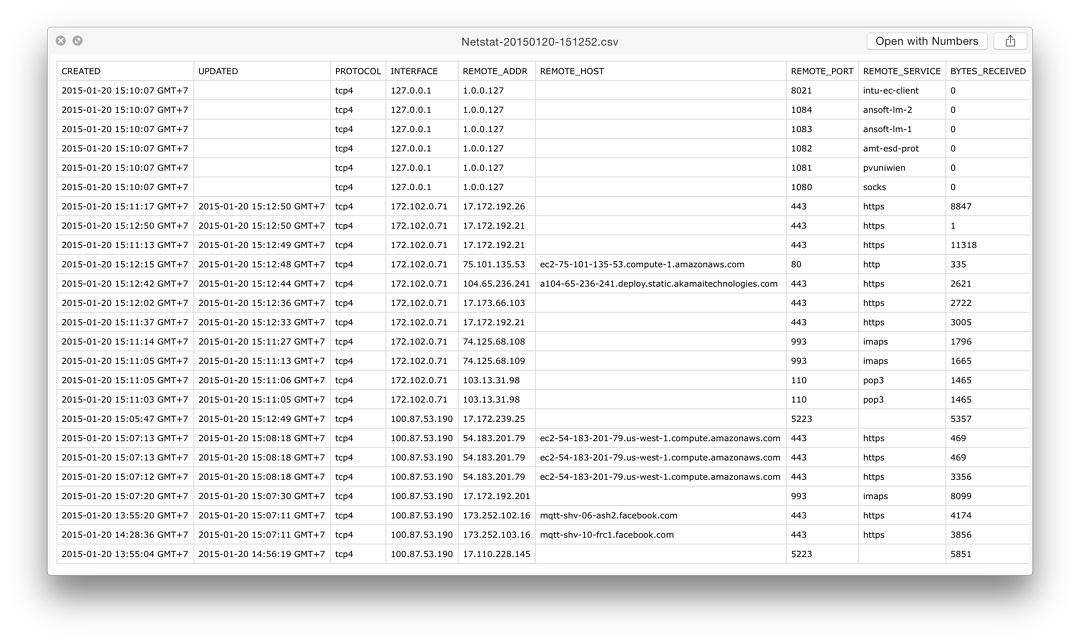
The full version was an in-app upgrade of $1.99 but I saw in the App Store that the whois feature could be added for $0.99, as could LAN Scan and Server Monitor support ($0.99 each).
The utilities I examined, mainly performed sub-par, with only Map of the Internet by Peer 1 Hosting, NETSTAT and InetTools - Network Diagnose Tools, considered adequate. These types of tools will not be valuable for all users, but as the internet grows, it will become more necessary to make checks in order to verify the safety of connections or to analyse links in use.
Graham K. Rogers teaches at the Faculty of Engineering, Mahidol University in Thailand where he is also Assistant Dean. He wrote in the Bangkok Post, Database supplement on IT subjects. For the last seven years of Database he wrote a column on Apple and Macs. He is now continuing that in the Bangkok Post supplement, Life. |
|

For further information, e-mail to
Back to
eXtensions
Back to
Home Page