Cassandra: Security Comment on Apple's Development of Multi-factor Authenticated Payment System

AMITIAE - Monday 12 September 2014
|
Cassandra: Security Comment on Apple's Development of Multi-factor Authenticated Payment System |
 |
|
|
By Graham K. Rogers
Much (virtual) print has been wasted on the security aspects by many commentators who presume that, following a poorly-reported security problem for some users of iCloud the previous week, Apple's customer safety with Apple Pay is also suspect. Comments by Eddy Cue when the service was announced, and by Tim Cook in an interview with Charlie Rose, are dismissed (whatever they might have said) because of course - it might be argued - they are biased. One thing that both referred to was the secure element that is available on the A8 processor. When the TouchID was introduced last year, the data was reported to be stored in a secure enclave on the A7. Derision, criticism and questions followed, but Apple satisfied most of its critics and thus far there have been no reports of security problems with this feature: especially thumbs surgically removed by criminal gangs as was theorised by some. The structure of the new processor is commented on by Ryan Smith of Anand Tech who analyses technical information on the A8 released by Apple.
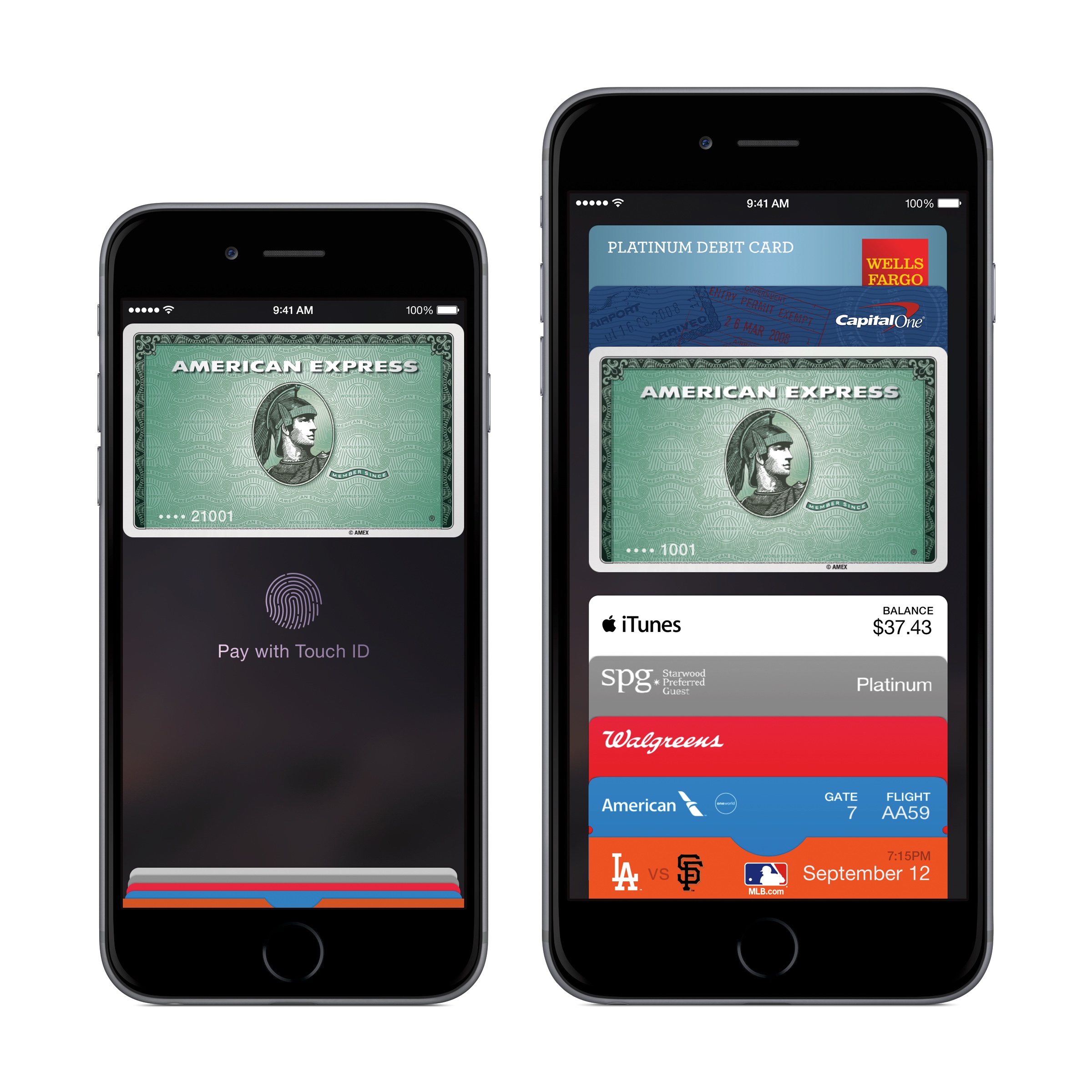
Apple Pay - Image Courtesy of Apple
Hope is not totally convinced about the success of the system in terms of speed, citing the London Underground attempts at using NFC on a number of occasions. However, he is carefully focused on the differences between the approach of Apple ("a for-profit company looking to deliver value to customers who pay money for that value") and Google, who launch "a bunch of technology into the marketplace and it leaves the creation of business models to someone else."
Graham K. Rogers teaches at the Faculty of Engineering, Mahidol University in Thailand where he is also Assistant Dean. He wrote in the Bangkok Post, Database supplement on IT subjects. For the last seven years of Database he wrote a column on Apple and Macs. He is now continuing that in the Bangkok Post supplement, Life. |
|

For further information, e-mail to
|

|