Cassandra: Fingerprinting and the iPhone

AMITIAE - Thursday 26 September 2013
|
Cassandra: Fingerprinting and the iPhone |
 |
|
|
By Graham K. Rogers
Practical BackgroundBack in the 1970s, I was a policeman in the UK, so not only did I take the fingerprints of several people, both working in a small station and later when I served as a detective for a short time. This was not as romantic or risky as the TV shows would have one believe. My main job was on the Motorways where I saw too many accidents; and riding large motorbikes: much more risky, and I have the scars to prove it.When a police officer joins, two sets of fingerprints are taken: one for local use, and one for Scotland Yard as the Metropolitan Police acts as coordinator (or did then) for fingerprint identification purposes between the different forces. When I left, the local fingerprints were returned, but not those that went to London. My Inspector denied these had ever existed.
The scene of a crime was rather different, as if there were fingerprints, these were only partial, or smudged and, despite what the TV suggests, the chances of lifting a perfect print are rather small. It does happen, of course, but that is more a question of luck. In the 1970s and beyond, prints from a crime scene had to be painstakingly matched to any on record. Then, it took an unusual skill because what the expert was looking for were comparisons that were so unusual that they could not, in combination, belong to any other finger. The way lines would meet, or break; the specific parts of a curve in a loop or a whorl; gaps in the line; scarred tissue. All of these would be used to build a picture and only when there were several points of comparison, was it accepted that these were the prints of the criminal (or the victim if this was being used for identification). If the prints were not on record, they might be taken if a suspect was arrested; or sets of prints from a crime might be sent on to Scotland Yard for another search to be conducted. One person, searching through hundreds of sets of prints to identify a criminal, could take days - even with a classification system that would limit the search - so moving the identification process to a computerised system was an obvious move when the technology became available. However, while fingerprint experts think in analogue terms - looking for a particular curve, for example - a computer works mathematically. And also much faster.
Technical DevelopmentNEC, for example developed the Minutiae and Related Method which is a matching algorithm. It uses ridges and minutiae inside a clear zone of fingerprints to achieve accurate fingerprint identification.
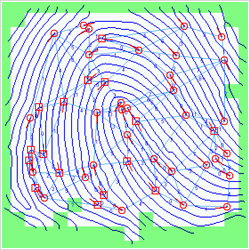
NEC - Minutiae and Related Method
A full description of the development and introduction of this system is available in Chapter 6 of The Fingerprint Sourcebook from the National Criminal Justice Reference Service PDF series on fingerprints, "Automated Fingerprint Identification System (AFIS)". The point about this and other systems used for fingerprint identification is that they use algorithms and not a stored image to work.
Fingerprint SecurityLike others I have used fingerprints to access computer systems, and with all biometric systems there is always a possibility that a clever operator could break in. The fear that Apple would send the data to the government was laid to rest (at least for some) fairly quickly, when it was pointed out that the mathematical data - not the fingerprint - was stored only on the device in a secure "enclave" on the A7 processor.This mathematical data is like the algorithms that NEC uses to identify prints and contains a complex coding system that - as in the systems used by law enforcement - make it impossible for a print to be misidentified. As confirmation of this, other unique body parts have been used, such as a cat's paw, or even a nipple (although how anyone would use an iPhone in a crowded mall, for example, with that as the security key, I am not sure. Fortunately, Apple allows several identifiers to be used for each device, so fingers on left and right hands are options, as is also identification for other members of a family. With the cachet of being first to break into a new Apple device as the real prize, a German group set about creating an artificial fingerprint from a high resolution image of a real fingerprint. This is not easy, it took me a few minutes just to be able to take a reasonable photograph of my prints (Scotland Yard already has a copy, so I am not overly concerned about this), but the process of creating a latex version might take longer. The one factor that is missing is the iPhone 5s. Apart from the point that I do not have one, and these are unlikely to arrive here for a few months in substantial numbers, to make the artificial fingerprint work with the sensor, a criminal (or the NSA - they are the current bad guys) must be holding my iPhone. If it were lost, the "wipe" command in Find my iPhone would put any data loss risk out of the window. If the criminal master-mind were holding me and threatening to cut off my finger, I think data on my iPhone would be the least of my worries. The use of a latent print, with its usual loss of quality compared to the original, makes the casual creation of such a break-in tool rather less likely than may have appeared in the video - impressive as that process was - that describes the method of making a fingerprint spoof that was able to fool Apple's Touch ID. The process video, and some comments on the way it was created may be found in an item by Frederic Lardinois on Tech Crunch.
Graham K. Rogers teaches at the Faculty of Engineering, Mahidol University in Thailand where he is also Assistant Dean. He wrote in the Bangkok Post, Database supplement on IT subjects. For the last seven years of Database he wrote a column on Apple and Macs. |
|

For further information, e-mail to
|

|